Cybersecurity is a significant challenge in the cloud environment with the rapidly evolving threat landscape. Furthermore, with more businesses adopting cloud computing and its amalgamation with emerging technologies, the challenges have increased correspondingly. Hence, the focus should be on identifying these next-gen cybersecurity challenges and preparing to overcome them.
Cloud computing has improved IT efficiency, flexibility, and scalability. However, all these features have one common challenge, security. The problem with cloud computing cybersecurity is that organizations must correctly distinguish where the CSP’s (Cloud Service Provider) responsibility ends and theirs begins. This gap increases the organization’s potential attack surface and enables malicious actors to infiltrate information systems. This article discusses next-gen challenges and risks and looks at how organizations can prepare themselves to overcome them to keep critical information assets’ confidentiality, integrity, and availability intact.

Traditional Cybersecurity Challenges in the Cloud
Since cloud computing came into being, many associated cybersecurity challenges have also attracted much concern. For example, data privacy in the cloud, misconfiguration-induced vulnerabilities, insider threats, and IAM (Identity & Access Management) issues are prominent among traditional cloud security challenges. In addition, technological advancements have integrated the cloud with many next-gen technologies, such as IoT (Internet of Things), Blockchain, 5G, etc. This new transformation has changed the face of cloud computing and increased the risk of cyber intrusion.
Next-Gen Challenges and Risks Facing Cloud Security
The following are the next-gen cybersecurity challenges cloud computing must address to keep cloud cybersecurity intact.
- Quantum Computing:
Quantum computing is poised to be the future of computing, but it is not without its challenges. For example, quantum computers will likely break current public key cryptography algorithms. Such factors can make systems using traditional cryptography highly vulnerable to attacks.
- Distributed Cloud and Shadow IT
Distributed cloud services could be the norm in the future. It decentralizes cloud management operations and makes computing easy by placing more control of the public cloud in the user’s hands. In addition, it allows consumers to decide on their data processing and storage. Thus, it takes care of issues like lack of visibility and transparency. However, not having a continuously updated inventory of IT resources being used in distributed cloud environments poses significant challenges, as it can create intrusion channels for threat actors. Similarily if IT does not meet the needs of the user, the distributed cloud offers a plethora of ways of helping the user directly, this should motivate IT to actively engage with the users to meet their needs and ensure proper configuration and security of services offered.
- Internet of Things (IoT)
IoT is an excellent concept that increases user convenience. However, it can backfire because IoT devices can be an organization’s most vulnerable assets. With more IoT devices connected to the cloud, the risks multiply. Cloud misconfigurations are common in IoT devices. Besides, users’ lack of basic cybersecurity hygiene could be a problem. IoT risks include broken access control, inappropriate logging, lack of monitoring, and broken authentication.
- Hybrid or Multi-Cloud
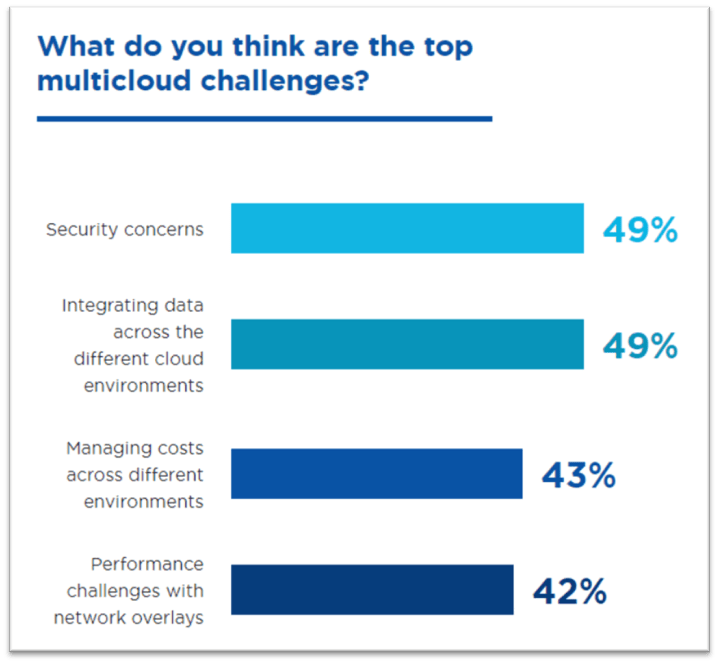
Businesses no longer depend on single cloud sources to avoid data dependency or vendor lock-in issues. Instead, they prefer a multi-cloud or a hybrid cloud environment because it offers greater scalability, flexibility, and resilience. However, adequate knowledge about hybrid cloud functioning is a significant challenge. Interoperability is also a major challenge in the multi-cloud environment. The absence of proper integration between the different cloud services allows malicious actors to sneak in and cause data breaches. As depicted in the graph below, Nutanix has highlighted organisations’ various multi-cloud challenges, with security concerns taking the top spot.
Businesses no longer depend on single cloud sources to avoid data dependency or vendor lock-in issues. They prefer a multi-cloud or a hybrid cloud environment because it offers greater scalability, flexibility, and resilience. However, the lack of adequate knowledge about hybrid cloud functioning is a significant challenge. Interoperability is also a major challenge in the multi-cloud environment. The absence of adequate integration between the different cloud services allows malicious actors to sneak in and cause data breaches. As depicted in the graph below, Nutanix has highlighted organisations’ various multi-cloud challenges, with security concerns taking the top spot.
How Organizations Can Prepare for the Next-Gen Cloud Security Challenges
The following solutions can go a long way to secure an organization’s cloud data from the next-gen cybersecurity challenges.
- Building ‘Zero-Trust’:
While users believe that corporate firewalls guarantee absolute safety, the Zero Trust concept presumes breach. It focuses on verifying each request as if it originated from an open network. So, the principle to follow is, “Always verify and Never trust.” Based on the above principle, the security policy ensures that each access request is authorized, authenticated, and encrypted before granting access. It applies least access principles such as the need-to-know, least privilege model, segregation of duties, and micro-segmentation to minimize lateral movement. Building a Zero Trust security model ensures using rich intelligence and analytics for detecting and responding to anomalies in real time.
- Exploring and Leveraging Quantum Computing:
Quantum computing promises to transform cybersecurity in the following ways, allowing organizations to prepare for next-gen security challenges.
- The pseudo-random number generators used in cryptography today are potentially open to compromise. Quantum computing enables quantum random number generation, which is fundamental to cryptography because they use quantum optics to ensure true randomness.
- Quantum key distribution employs quantum mechanics to ensure the secret exchange of encryption keys and allows secure communication. This technology can alert the presence of an eavesdropper.
- Quantum computing offers the potential to break the RSA algorithm, the most widely used public-key cryptography system, to secure data transmission. While the technology will take time to manifest, developing algorithms that are not immediately vulnerable to quantum computers is essential.
- Serverless Technology
A report from Grand View Research, predicts the global serverless architecture market size of USD 19.84 Billion by 2025
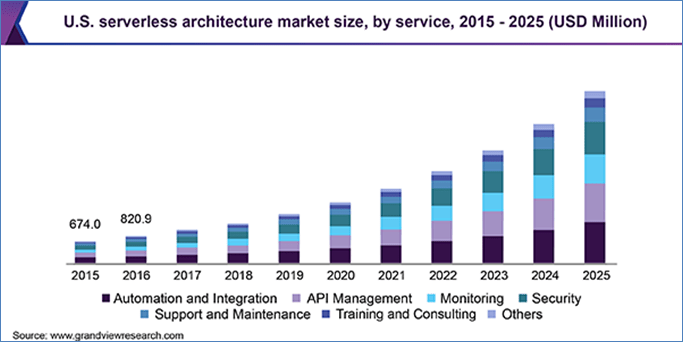
Other research suggests that the global serverless computing market is expected to witness a growth rate of 28.2% between 2020 and 2030. Using serverless technology is becoming the norm, allowing organizations to create better code for their applications. However, it requires shifting specific responsibilities such as patching, capacity management, and availability to CSPs (Cloud Solution Providers) like Microsoft Azure, Alibaba Cloud or AWS. While misconfigurations and unsecured coding practices remain the most prominent risks, businesses should focus on securing vulnerable points by adopting solutions that have the utmost interoperability.
- AI/ML applications in Cloud Architecture
According to research, artificial intelligence in the cybersecurity market is projected to generate a revenue worth $101.8 Billion by 2030. AI and ML have revolutionized cybersecurity by enabling the detection and blocking of advanced cyberattacks. Firstly, AI is useful in big data processing as it allows trawling through historical data to identify attack patterns. Secondly, AI/ML is valuable in predicting the safety of information systems. However, predictive analysis needs more time to become a powerful tool to provide effective cloud cybersecurity. Another area where AI/ML can prove helpful is the ability to provide automated responses. While AI/ML has the potential to revolutionize cybersecurity, much work needs to be done in this direction before using AI/ML applications in cloud architecture effectively.
- Shared Responsibility Model
The shared responsibility model of cloud cybersecurity delineates the responsibilities of the CSPs and the consumers. It envisages that the provider is responsible for the security ‘of’ the cloud, whereas the user is responsible for guarding data ‘in’ the cloud. So, the CSP’s responsibilities are securing the infrastructure, the operating systems, and virtualization layers and guaranteeing physical security. The customer’s responsibilities include application management, network configuration, and encryption.
- Watch Out for the Latest Development in Technology and Security Space
Organizations and executives should keep a watch on the latest developments in cybersecurity and emerging technology space. You may follow guidelines and processes suggested by organizations like NIST (National Institute of Standards and Technology) or CIS (Center for Internet Security). For example, recently, NIST published their Post-Quantum Cryptography Standardization Process on how organizations can prepare for upcoming challenges.
Thus, besides looking at the various IaaS, PaaS, and SaaS aspects, one also needs to remember the importance of cybersecurity-as-a-service (CaaS) as well. Therefore, organizations should concentrate on these aspects to prepare for facing and overcoming the next-gen challenges in cloud environment cybersecurity.
Final Words
As more business entities and organizations adopt cloud technology to offer higher reach and flexibility, cloud security magnitudes are also growing. An effective cloud cybersecurity strategy requires a clear distinction between CSP and consumer responsibilities. This delineation ensures data privacy and can prevent malicious actors from taking advantage of gap vulnerabilities. Besides, organizations must employ advanced solutions that leverage today’s emerging technologies, such as AI and Blockchain, along with the right set of policies, such as Zero-trust principles, to combat cloud cybersecurity challenges.
References
- Chukwube, J. (2021, August 26). How to Prepare for the Next Generation of Cloud Security. Techopedia. https://www.techopedia.com/how-to-prepare-for-the-next-generation-of-cloud-security/2/34574
- Shea, S. (2021, February). Top 11 cloud security challenges and how to combat them. SearchSecurity; TechTarget. https://www.techtarget.com/searchsecurity/tip/Top-11-cloud-security-challenges-and-how-to-combat-them
- Online, D. (2021, November 2). Data sovereignty: A critical consideration in your cloud strategy. DATAQUEST.
- Statista. (2022, August 30). Global number of quarterly data breaches 2021-2022. https://www.statista.com/statistics/1307426/number-of-data-breaches-worldwide/
- Brookes, H. (2021, November 16). Quantum computers: Opportunities, risks, and challenges for policymakers.
- American University. https://www.american.edu/sis/centers/security-technology/quantum-computers.cfm
- Microsoft.com. Embrace proactive security with Zero Trust. https://www.microsoft.com/en-us/security/business/zero-trust
- Lipman, P. (2021, January 4). How quantum computing will transform cybersecurity. Forbes.
- Brode, B. (2021, February 1). AI no silver bullet for cloud security, but here’s how it can help. InfoQ. https://www.infoq.com/articles/ai-cloud-security/
- Bernhard, T. (2021, October 7). Understanding the shared responsibility model for cloud security. CloudCheckr. https://cloudcheckr.com/cloud-security/shared-responsibility-model/
- AI in cyber security market worth $101.8 billion by 2030. (n.d.). P&S Intelligence. Retrieved September 13, 2022, from https://www.psmarketresearch.com/press-release/artificial-intelligence-in-cyber-security-market
- Serverless computing market rising trends, technology research and precise outlook 2022-2030. (2022, June 9). Digital Journal; Digital Journal Inc. https://www.digitaljournal.com/pr/serverless-computing-market-rising-trends-technology-research-and-precise-outlook-2022-2030
- Lange, T., & Steinwandt, R. (Eds.). (2018). Post-quantum cryptography: 9Th international conference, PQCrypto 2018, Fort Lauderdale, FL, USA, April 9-11, 2018, proceedings (1st ed.). Springer International Publishing. https://csrc.nist.gov/projects/post-quantum-cryptography
- Serverless architecture market size worth $19.84 billion by 2025: Grand View research, inc. (2018, December 5). PR Newswire. https://www.prnewswire.com/news-releases/serverless-architecture-market-size-worth-19-84-billion-by-2025-grand-view-research-inc–835575953.html

[…] The metaverse is much like the internet: an open source, decentralized platform for managing all of our virtual identities and assets. But in order to create a truly interoperable system, it will need to be both open source and secure—with users comfortable using personal data within this environment. […]
LikeLike
[…] ever scratched your head about the cloud scene in China or pondered over the challenges of cybersecurity in our cloud-driven world, you’re in for a treat. Oh, and for those fascinated by the blend of artificial intelligence […]
LikeLike
[…] Omni Cloud Strategies: The New Digital Frontier – Part 1 Introduction to Omni Cloud & The Rise of Multi-Cloud Environments Your Cloud journey and how to balance developer autonomy, platform manageability and security Cybersecurity and Cloud: Next-Gen Challenges and Risks and How Organizations Can Prepare Themse… […]
LikeLike