Now we’ll look at configuring SAML integration between VMware Identity Manager and Salesforce for Workspace ONE.
Definition: Security Assertion Markup Language (SAML). It is an open standard which enables SSO for many different services and platforms. Authenticating with SAML allows a user to log in once per session.
Here are the defining components of SAML:
- Service provider (i.e. an application.)
- Identity provider (who is authenticated, and what authentication methods are used.)
- End user who is accessing over SAML.
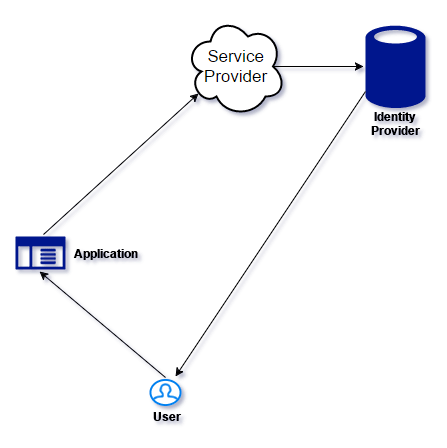
- User starts the SAML Application
- Service Provider (SP) sends a request to the Identity Provider (IdP) for authentication
- If the user is not authenticated, the IdP requests authentication from the user. (I.e. username and password)
- The IdP then sends response to the SP with a token for that user.





