Information security aspects when moving operations from on-premise
So if you are reading this I will make some basic assumptions that you know about Microsoft Azure, Amazon Web Services and perhaps even Alibaba Cloud, these are renowned hyperscale cloud vendors. Last few years cloud computing have been among the IT industries hottest topics. The term refers to on-demand access to computing resources provisioned by another provider. 2019 has been dubbed the year of migrations by several vendors and a pronounced advantage of cloud computing is that they tend to be highly available and easily scalable. For fast-growing business, cloud-computing has revolutionized the way they can work. Organizations typically lease cloud-based resources from outside the organization. Of course, it is also possible (but not as common) to host cloud-based services internally.
While cloud computing can be very cost-efficient and offer fast scaling, it’s challenged by the fact that resources will most likely be hosted outside of the business’ data centre and therefore, outside of the direct control of that business, increasing the complexity to manage risk and handle governance.
When migrating services to cloud-based providers outside their own premises, organizations must ensure that proper security management is in place to prevent unauthorized access to or modification of the data. These requirements should be formally defined. As an example, the Department of Defense Cloud Computing Security Requirements Guide defines specific requirements for U.S. government agencies to follow when planning the use of cloud-based assets. This document identifies requirements for assets according to their classification on six different levels. Similar guidelines should be put in place in all organizations with regulations and internal procedures that may apply, such as the European GDPR.

In general, a sound information security program should be in place that these requirements can be integrated into. This program should naturally cater to all regulatory and compliance requirements the business itself is subjected to. When standards, procedures, policies, and guidelines are in place and data and systems to be moved have been properly classified, the right cloud service provider (CSP) for the organization should be chosen according to these deducted requirements.
While Amazon Web Services, Alibaba Cloud and Microsoft Azure are the big players in the field, they still have to be properly checked for compliance issues with any particular business. While big players generally will try to adhere to any applying law such as GDPR, regional peculiarities might not suit all business models and even cause  downright conflict. For example, it has to be kept in mind that all US-based cloud providers will have to adhere to the Patriot Act of 2011. This may in itself be directly opposed to the EU data protection laws of GDPR if a migration organization is EU based. It has been shown that in a conflict situation, US providers will generally adhere to their home country law first, which may put EU organizations in difficult situations, as their cloud provider will inadvertently not comply with EU law.
downright conflict. For example, it has to be kept in mind that all US-based cloud providers will have to adhere to the Patriot Act of 2011. This may in itself be directly opposed to the EU data protection laws of GDPR if a migration organization is EU based. It has been shown that in a conflict situation, US providers will generally adhere to their home country law first, which may put EU organizations in difficult situations, as their cloud provider will inadvertently not comply with EU law.
For smaller cloud providers, data centre security must be checked thoroughly. Data centres should be safe, secure and audited and operating redundantly in geographically spaced out locations for disaster prevention. In case an organization does not want to check and audit these facts themselves, certificates according to, for example, ISO 27001 is a big help.
As is obvious, the integrity and confidentiality of the information stored in the cloud, as well as the availability of provisioned systems, should be an organization primary concern when migrating to cloud-based services. Data loss, outages, loss of confidentiality and unauthorized modification of data or code must be prevented. Also, adherence to local and international laws and regulations has to be thoroughly checked. If an organization uses a federated or single-sign-on identity management system, it should be planned to properly extend this to the cloud services to not introduce new attack vectors by adding a new authentication layer. If sensitive or confidential data is handled, encryption should as well be mandatory.
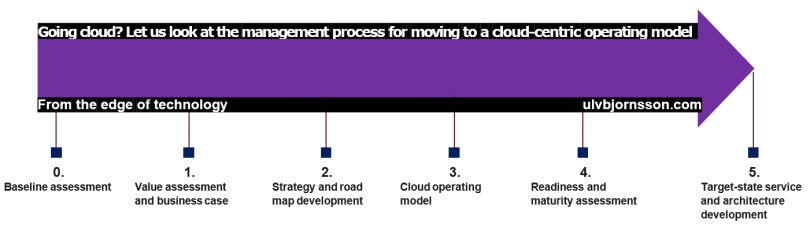
Now achieving this is a daunting undertaking, companies may very well be used to ITIL, COBIT and variations of TOGAF implemented throughout the enterprise for their on-premise digital estate but for a cloud world, you need to change your operating models, processes and skillset.
So to gain the benefit of the cloud, going agile is key but also having the correct governance in place, the processes and the tools to see whether or not you are compliant with what you have implemented. It is key to collaborate with those who have walked the path before you so that you can avoid the pitfalls and instead accelerate your cloud journey.
What are the benefits?
So you manage on your own or with the help of a partner to adopt a set of rules, processes and an overall governance model whilst also implementing an agile mindset in your organisation. What do you gain?
1. FASTER TIME TO MARKET
2. BUILD THE RIGHT PRODUCTS
3. EARLY RISK REDUCTION
4. QUALITY
5. CULTURE AND MORALE
6. EFFICIENCY
7. EMERGENT OUTCOMES
8. PREDICTABILITY
9. COST CONTROL
10. SCALE
11. TRANSITION TO DIGITAL INNOVATION
Do you agree? If not, why? What is it you think is most important when starting on a cloud journey, let me know on Twitter @UlvBjornsson or down below in the comment section. If you need any advise or want to discuss your cloud journey with me, reach out!
This is first in a series on cloud journey guidance for decisionmakers we will be starting off high-level and then diving in more depth with each area so stay tuned whether you are a technical decision maker or a business decision maker, getting an overview of the complete picture is vital to ensure that when you do pull the trigger on a decision you will be able to see five steps ahead and steer accordingly.
[…] are a wide variety of ways to run a Blockchain, for the enterprise more and more turn to the cloud leveraging Blockchain as a Service, this is offered by Alibaba Cloud, Microsoft and other […]
LikeLike
[…] are a continuum of tasks, projects and initiatives, therein you build natively in Cloud and also migrate workloads into Azure, securing and protecting those workloads so that they are robust and resilient. You then proceed to […]
LikeLike
[…] the cloud, whereas the user is responsible for guarding data ‘in’ the cloud. So, the CSP’s responsibilities are securing the infrastructure, the operating systems, and virtualization layers and guaranteeing […]
LikeLike