For as long as it has been in development inside the science labs of the universities, corporations and government agencies, quantum computing has been considered the next frontier in cybersecurity. Quantum computers are machines that do not work with classical electrical on and off-states but instead rely on quantum states that can be in several states at once, a circumstance known as „superposition(1)“. While they are still in their very infancy, their capabilities have been mystified over and over and it’s probably fair to say that quantum computing is one of the most misunderstood technological advancements of our day and age.
Some applications of quantum computers, like true random number generation, are already in use today. Others, such as machines capable of rapidly factoring large prime numbers, have yet to be realized. However, since the potential impact behind these developments is so immense the number of resources engaged in their development has been steadily increasing over the last decade.
True random number generation is bigger than it seems at first glance. Today’s computers can’t provide real randomness because of their deterministic nature. The best a classical computer can do is generate a so-called pseudo-random number from a series of calculations by a pre-defined algorithm. However, this requires an initial number, called a seed, to work off from, usually provided by performing calculations on the current date and time down to the milliseconds or by working with user input, or both. The problem with this is that for any given input, the output will always be the same. This is a problem when using one-time symmetric keys because if an attacker knows the algorithm he might be able to predict the seed number and therefore also calculate the encryption key. The indeterminacy of quantum computing can change this and provide for true random number generators and therefore, literally unbreakable one-time-pad symmetric encryption.
One of the most talked-about and feared aspects of quantum computers is their potential to eventually revolutionize cryptanalysis, the breaking of encryption schemes. Essentially, this boils down to the supposed ability of quantum machines to work on some calculations in a very parallelized and fast manner. As of today, there are basically two known cryptanalysis algorithms that would benefit massively from quantum computers with increased processing capacity. These are Grovers Algorithm and Shor’s Algorithm. The latter one is a method of factoring large prime numbers in polynomial time, essentially breaking asymmetric encryption schemes that rely on these large primes, like RSA. So far, Shor’s algorithm is not practically usable since breaking a prime of size n would require a machine log(n) qubits(2). So far, the largest known working quantum computer at IBM operates at 20 qubits(2), which is no danger yet for the large primes used in encryption schemes today. The Grover Algorithm is actually a method for searching in data but can be used for cryptanalysis in what is known as a known-plaintext attack. If a cryptanalyst has a ciphertext and can capture but a sample of the plaintext a quantum computer using Grover’s algorithm would essentially be able to try combinations in a fast manner, effectively doubling the attack speed compared to today’s methods. However, while this problem is described scientifically sound in theory, no known implementation of Grover’s algorithm exists to date, yet.
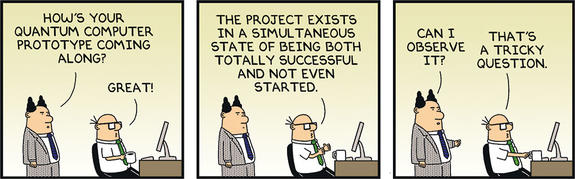
As can be told from all of these facts, quantum computers are not quite a threat yet in 2019. However, the technology is surely advancing and quantum-proofing applications today with what is called post-quantum cryptography is an important part of what would be deemed to be called perfect forward secrecy. If today’s asymmetric and prime-reliant symmetric algorithms are indeed rendered obsolete by able quantum machines it will prove a wise choice to not be pressed to update existing software and processes in a hurry.
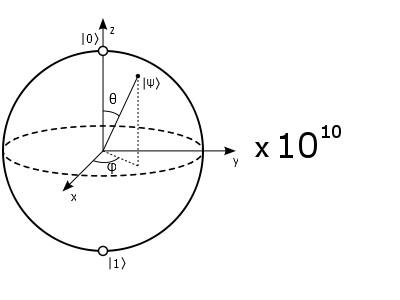
Superposition (1)
Multiple states at the same time — something that can be “here” and “there,” or “up” and “down” simultaneouslyQubit (2)
In all honesty Qubit.. Does sounds like something you’d name a yoghurt marketed to kids. Encode the zero and the one into two distinguishable quantum states. And since yogh… These states behave quantum(ly) we capitalize on the phenomena of “superposition” and “entanglement.”Entanglement (3)
A strong correlation that exists between quantum particles — picture Conjoiners, or a hive mind. Inextricably linked in perfect unison, even if separated by great distance.
In my next article, I will talk about quantum cryptography and cryptography in a post-quantum world. Are you worried or excited about a world in which we have quantum computing? Let me know what you think either in the comment field below or over on Twitter @UlvBjornsson

[…] in my previous article on quantum computing, we talked about where we are today, and where we are headed in regards to breakthroughs in the […]
LikeLike
[…] Cybercrime is forecast to reach $10.5 trillion by 2025. The sheer volume and increasing sophistication of cyberattacks has made security analysis untenable. […]
LikeLike
[…] Quantum computing is poised to be the future of computing, but it is not without its challenges. For example, quantum computers will likely break current public key cryptography algorithms. Such factors can make systems using traditional cryptography highly vulnerable to attacks. […]
LikeLike