AirWatch, it’s here to stay.
So let’s talk about AirWatch, Office 365 and Powershell.
Objective: To enable integration between Powershell and Office 365 to facilitate; AirWatch Mobile Email Management (MEM).
“Mobile Email Management (MEM) functionality in AirWatch delivers comprehensive security for your corporate email infrastructure by allowing only compliant users and devices to access email.”

Now to getting this up and running
The steps we will be taking are
- Integrate PowerShell with AirWatch
- Setting up a PowerShell Admin User
- Enable Powershell Integration in AirWatch
- Configure Exchange to Block or Quarantine Devices
- Email Management
- Cmdlets Executed by AirWatch
Integrating Powershell with AirWatch
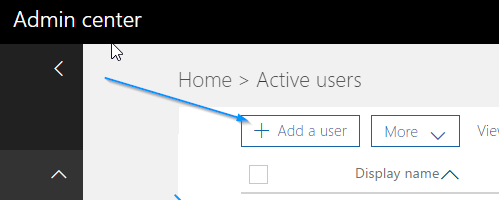
1. Log into your Office 365 (portal.office.com) as an Administrator
2. Navigate to Active Users

3. Add a User
4. Give the Service Account a name, preferably a descriptive name ahering to a naming standard. We called it svc.memairwatch
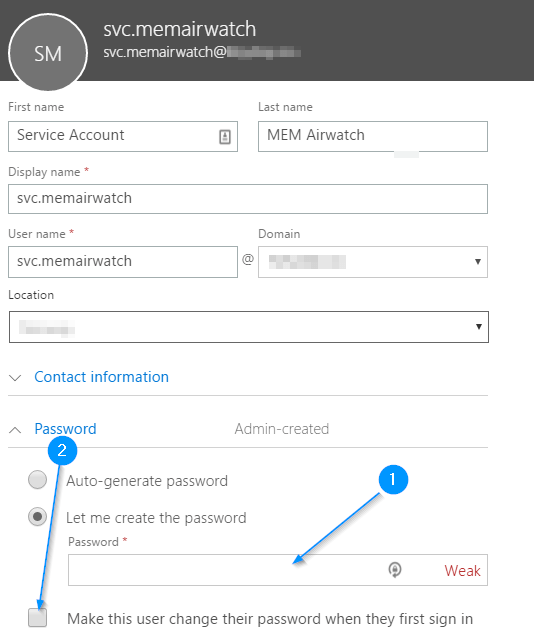
5. Generate a password for the Service Account, utilizing the generator of your choice, or random mashing on the keyboard. I prefer using Norton’s Password Generator: here
You want the password to remain static, unless you have a process for updating service accounts.
6. Click “Add” to add the user, if it’s been given a license, you can remove it as this service account does not require a license.

7. Now we need to assign rights and permissions to the Service Account, we do this by going to the “Exchange Admin Center”
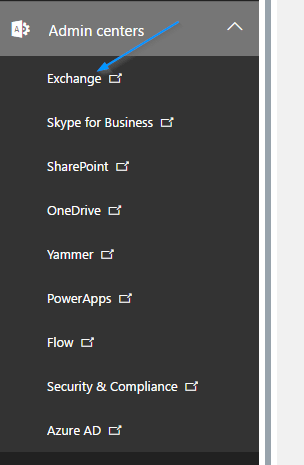
8. Choose the “Permissions“-tab and “admin roles”

9. We are going to create a unique admin role for the Airwatch MEM Service Account, following the principle of least privilege which translates to “lowest level of user rights that they can have and still do their jobs.”
10. Choosing the + whilst under the “permissions” -> “admin roles” will open the
“new role group”-window
11. “Roles” you want to add “Mail Recipients”, “Organization Client Access” & “Recipient Policies”.
12. Under “Members” you add the “Service Account” that we created earlier.
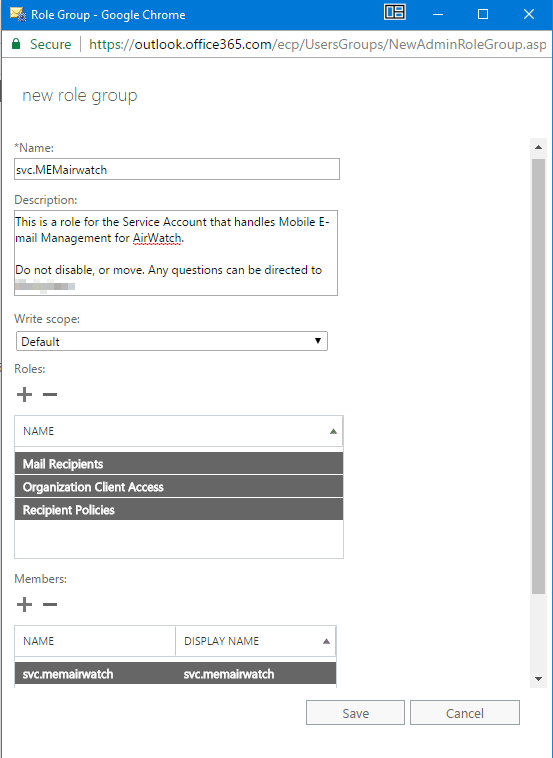
13. Hit “Save”.
Now we move over to the AirWatch-console. Log in as an account with administrator-rights.
1. Navigate to “Devices -> Profiles & Resources -> Profiles”
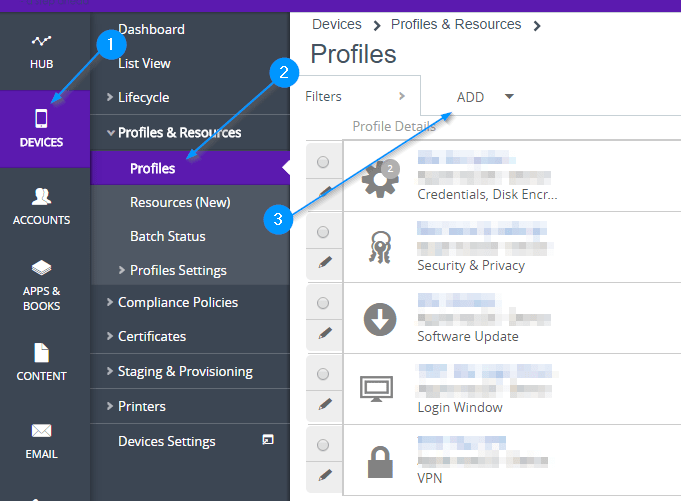
2. Hit “Add“
3. Choose your platform for deployment of the e-mail profile.
For this example we’ll be demonstrating this with Apple iOS.

4. First tab “General” give the profile a logical name, plan for what it’ll be like if you are managing hundreds, or thousands of devices. We named it iOS: Mobile Email Management.

5. In “Assigned Smart Groups” you can create or select a smart group that you’ll apply the profile to. You can filter the smart group to target device OS, less/equal/greater than and pinpoint exactly what devices are members of it. Allowing greater flexibility and less administering.
6. Now click “Exchange ActiveSync” and then choose “Configure” under “Mail Client” you choose the client you’ll be supporting. We are going with “AirWatch Inbox” for this setup.
Since our setup is Office 365, the Exchange ActiveSync Host(1) is set to outlook.office365.com
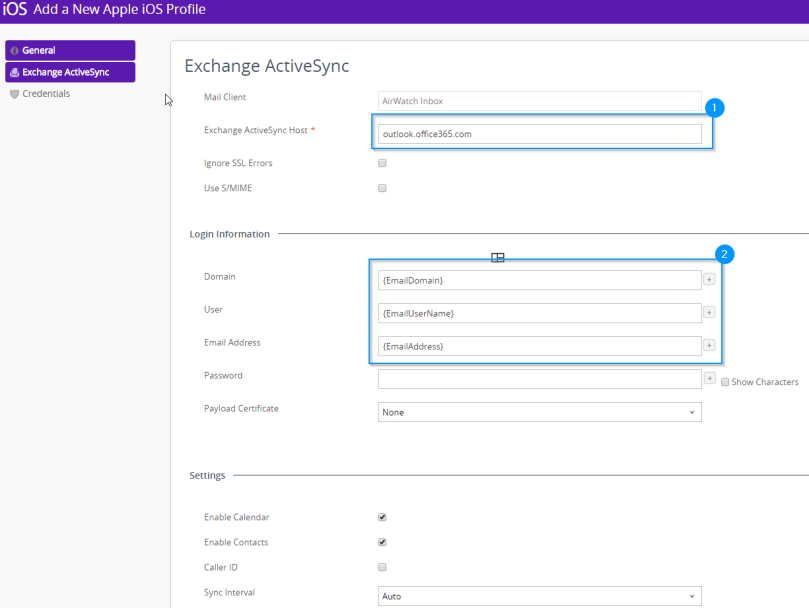
7. In “Login Information” you need to ensure that the “Domain“, “User” and “Email Address” reflects the naming conventions you have in your infrastructure. For this customer we configured the following patterns as they reflect the username and naming conventions in this environment.
8. These are the settings you can configure for AirWatch Inbox, since the defaults are fine we are leaving it at that, but know what they are and see how you can adapt or tailor it for you environment.
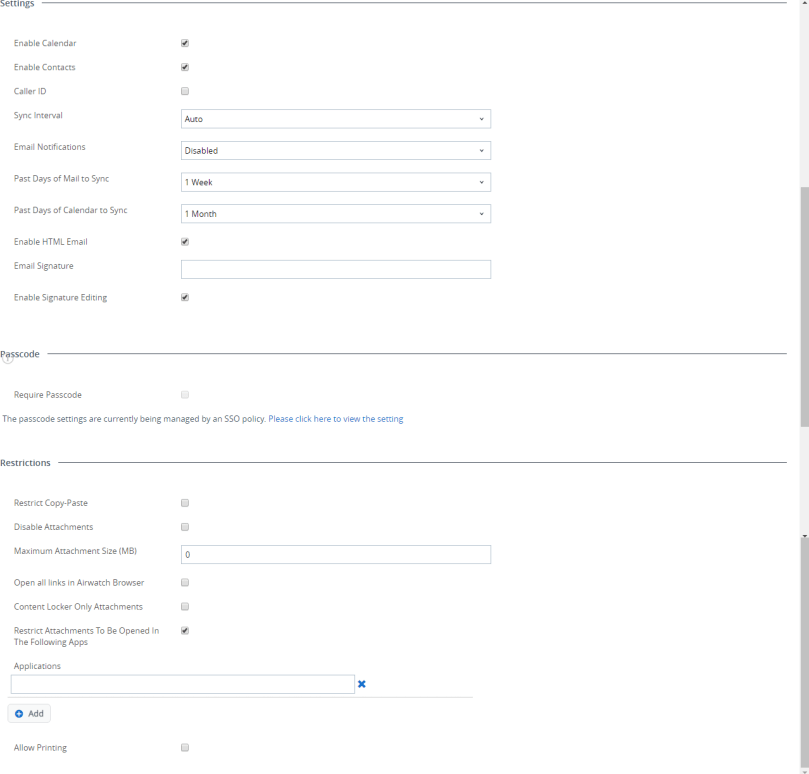
9. When you are done, hit “Save & Publish“.
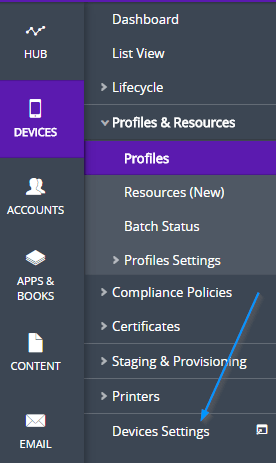
Next up we are moving over to “Devices Settings” we need to configure the “Email > Configuration” and the integration between the AirWatch console and the O365 platform as well as the MEM Profile Deployment.
- Hit “Devices Settings”
2. Choose “Email” and “Configuration”

Upon “Configuration” you get this: 
“Mobile EmailManagement (MEM) functionality in AirWatch delivers comprehensive security for your corporate email infrastructure by allowing only compliant users and devices to access email.
1) Platform Since we are doing this on O365, and we are setting up a SaaS-solution (Cloud AirWatch) with O365 (SaaS) we are choosing “Deployment Model” – “Direct” and “Email Type” is “Exchange” with “Exchange Version” set to “Exchange Office 365″
Since we are doing this on O365, and we are setting up a SaaS-solution (Cloud AirWatch) with O365 (SaaS) we are choosing “Deployment Model” – “Direct” and “Email Type” is “Exchange” with “Exchange Version” set to “Exchange Office 365″
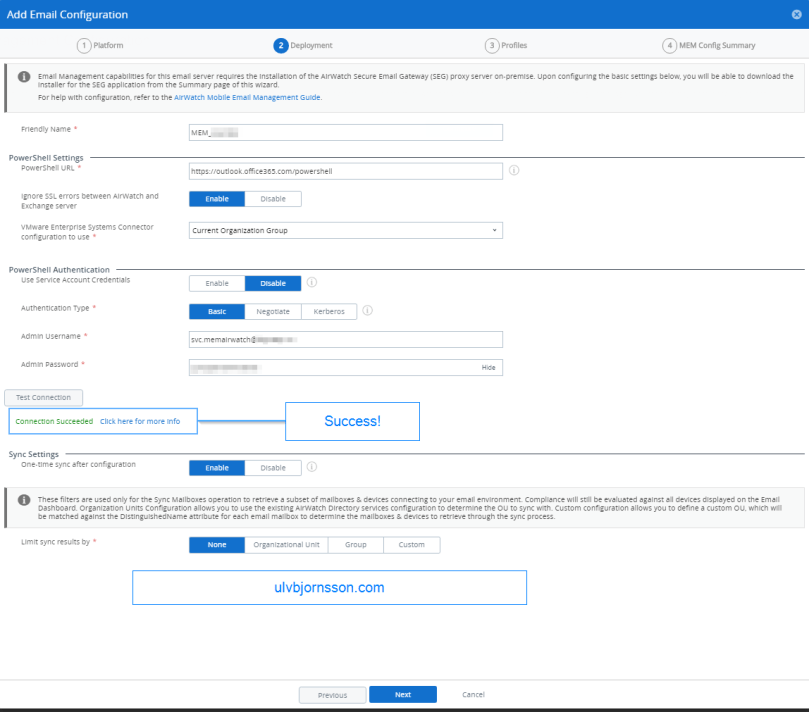
2) Deployment
3) Profiles
 Friendly Name: MEM_O365
Friendly Name: MEM_O365
Powershell URL: https://outlook.office365.com/PowerShell
Authentication Type: Basic
Admin Username: “Serviceaccount”@”domain.com”
Admin Password: “Service account password.”
(This is what we previously setup in part 1)
4) MEM Config Summary

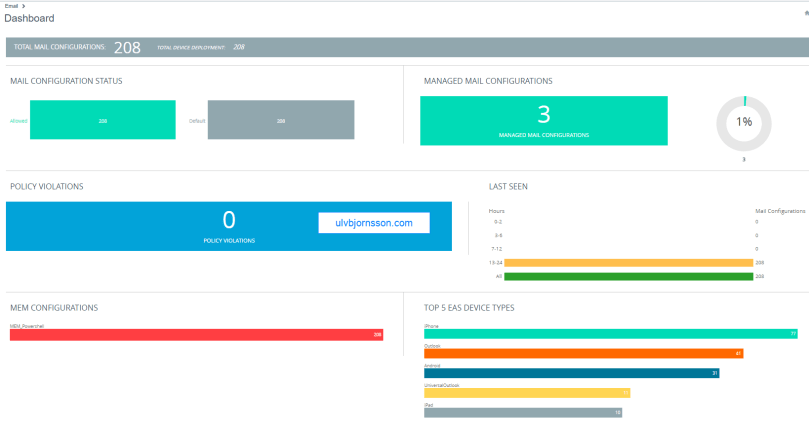
Now after the Powershell MEM EAS collection has completed it feeds you back the information in this dashboard:
Success, you can now start configuring your compliance profiles to suit your needs.
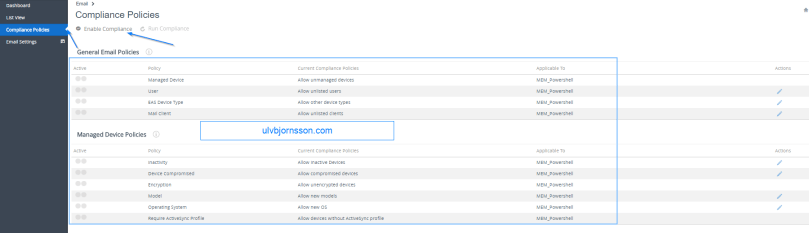
Be careful to not initiate anything, without being sure of what it will do.
Last but not least the cmdlets that it’s being run through this integration:
New-PSSession
- Creates a persistent PowerShell connection to a local or remote host. Once the session is open, the client can perform any number of PowerShell commands.
- Performs Set-CASMailbox and updates three distinct parameters for a mailbox when AirWatch uses this connection: ActiveSyncAllowedDeviceIDs, ActiveSyncBlockedDeviceIDs, and ActiveSyncEnabled.For example:
- New-PSSessionOption -SkipRevocationCheck -SkipCACheck -SkipCNCheck–ProxyAccessType WinHttpConfig
- New-PSSession –ConfigurationName $configurationName -ConnectionUri $connectionUri -Credential $cred -Authentication $authentication-AllowRedirection -SessionOption $proxyOption
Import-PSSession
Provides the ability to import PowerShell commands from one PowerShell session to another. For example:
- Import-PSSession –AllowClobber -CommandName $commandToImport -FormatTypeName
Set-ExecutionPolicy
Allows the client to modify its preferences for the PowerShell execution policy. Set-ExecutionPolicy also helps to determine if the client has the permissions necessary to perform certain PowerShell commands.
Set-CASMailbox
Provides the ability to block or allow client access to specific user’s mailboxes over a number of different client applications, including ActiveSync. Using this cmdlet, AirWatch can block particular devices or users from accessing ActiveSync based on the device compliance and user compliance to MDM policies. AirWatch specifically leverages the following arguments to this cmdlet. For example:
- Set-CASMailbox “acmeuser” – ActiveSyncAllowedDeviceIDs{Appl123456ABCD78} – ActiveSyncBlockedDeviceIDs $null – ActiveSyncEnabled $true
Note: The Set-CASMailbox cmdlet operates on one mailbox at a time and can configure properties for Exchange ActiveSync. You can configure a single property or multiple properties by using one statement.
- ActiveSyncAllowedDeviceIDs – Provides the ability to whitelist particular device IDs that can access the mailbox through ActiveSync. The ActiveSyncAllowedDeviceIDs parameter accepts a list of device IDs that are allowed to synchronize with the mailbox.
- ActiveSyncBlockedDeviceIDs – Provides the ability to blacklist particular device IDs that cannot access the mailbox using ActiveSync. The ActiveSyncBlockedDeviceIDs parameter accepts a list of device IDs that aren’t allowed to synchronize with the mailbox.
- ActiveSyncEnabled – Provides the ability to completely enable or disable ActiveSync access for a particular mailbox. TheActiveSyncEnabled parameter specifies whether to enable Exchange ActiveSync.
Get-CASMailbox
Returns a complete list of attributes of a mailbox. This is also used for performing one time sync of mailbox. For example:
- Get-CASMailbox “acmeuser”|Select ActiveSyncAllowedDeviceIDs,ActiveSyncBlockedDeviceIDs
- Get-CASMailbox –Filter $filter $–ResultSize Unlimited
- Get-CasMailbox –Identity $identity
Set-ADServer Settings
- Set-AdServerSettings –ViewEntireForest $true/$false
Get-ActiveSyncDevice
Retrieves a list of devices in your organization that have active Microsoft Exchange ActiveSync partnerships. This is also used for performing one time sync of mailbox. Administrators should now select the Exchange 2010 MEMconfig option for ‘Get-ActiveSyncDevice’, and the Exchange 2013/Office 365 option for ‘Get-MobileDevice’.
For Exchange 2010:
- Get – ActiveSyncDevice –Mailbox “acmeuser”
- Get-ActiveSyncDevice –ResultSize Unlimited
- Get-ActiveSyncDevice –Mailbox $mailbox
For Exchange 2013/2016/Office 365:
- Get-MobileDevice –Mailbox “acmeuser”
- Get-MobileDevice –ResultSize Unlimited
- Get-MobileDevice –Mailbox $mailbox
AW-Get-ADGroups
The Get-ADGroup cmdlet gets a group or performs a search to retrieve multiple groups from an Active Directory. For example:
- Get-OrganizationalUnit
Clear-ActiveSyncDevice
Deletes all user data from a mobile phone the next time that the device receives data from the server (for example, syncs with Microsoft Exchange Server 2010). Sets the DeviceWipeStatus parameter to $true in Exchange. For example:
- Clear-ActiveSyncDevice –Identity $identity –Confirm $true/$false
Remove-PSSession
Closes or ends Windows PowerShell session(s).
That’s it for this integrating VMware AirWatch with Powershell and enabling Mobile Email Management.
As always hit me up on Twitter if you have suggestions, feedback or questions @UlvBjornsson

Very impressive!
LikeLike
Thank you for your kind feedback, Willy!
LikeLike
Hi.
1. How about mobile device side of things? What needs to be done there (Such as download agent, run it,…)?
2. Can it be updated to reflect recent changes such as “inbox” app going away, its replacement, how to connect email?
Thanks
LikeLiked by 1 person
If you have configured your AirWatch tenant, enrollment, policies, and the Office 365 (or collaboration client) and other options you wish to reflect on your device. The next step will be to enroll it to your AirWatch. So either this is tied to the device or it is user intiated. I will assume it is user intiated in this case.
Navigate to AWAgent.com from the native browser on the device that you are enrolling.
AirWatch auto-detects if the AirWatch Agent is already installed and redirects to the appropriate mobile app store to download the Agent if needed.
Downloading the Agent from public application stores requires either an Apple ID or a Google Account.
Run the Agent upon the completion of the download or return to your browser session.
Important:
To ensure a successful installation and running of the AirWatch Agent on your Android device, it must have a minimum of 60 MB of space available. CPU and Run Time Memory are allocated per app on the Android platform. If an app uses more than allocated, Android devices optimize themselves by killing the app.
Enter your email address. AirWatch checks if your address has been previously added to the environment. In which case, you are already configured as an end user and your organization group is already assigned.
If AirWatch cannot identify you as an end user based on your email address, you are prompted to enter your Environment URL, Group ID, and Credentials. If your environment URL and Group ID are needed, your AirWatch Administrator can provide it.
Finalize the enrollment by following all remaining prompts.
LikeLike
Thanks for posting this Ulv. One question – we have a single O365 Exchange tenant with multiple companies with their own email domains – all in hybrid mode (while we migrate). If each one has it’s own Aiwatch Cloud Connector can Airwatch support having multiple ACC’s under a single instance of Airwatch? Ow will each company need its own instance of Airwatch?
LikeLiked by 1 person
Hello Julian,
This depends primarily on the level of granularity and segregation you want between each company. Is it okay for them to share? Or are there any limitations/compliance requirements. If they can share, you can add multiple domains. Do you have a cloud (SaaS) Airwatch or an on-premise Airwatch?
LikeLike
Excellent, what a website it is! This website provides useful facts to us, keep it up.|
LikeLike
We currently have this configured, but the only issue is that we have to use the native mail app since the Outlook app is not an option under the profiles. Is there a way when adding Outlook as a managed app to integrate with Powershell to auto un-quarantine a device? Seems like the Powershell integration only works with Device Profiles.
LikeLiked by 1 person
Auto-unquarantine devices via PowerShell would be doable but may be over engineering it, I think you are right in your observation that the PowerShell integration now likely requires device profiles (but device profile in o365 context vs airwatch context are separate things, back when I did it, it was over EAS and a service account that let’s you set device profiles that are supported (in airwatch) make changes over EAS and PowerShell.
LikeLike
When a managed device uses Outlook app, in the exchange, no device model will be listed instead it is listed as “Outlook for iOS and Android” and the EAS sync back to MDM with outlook as a device itself listed as an unmanaged device. Because of no device model/details, MDM have placed the “Outlook” as unmanaged.
Is there a work around to this?
LikeLike
Great question, and I sadly don’t have an environment where I can test but my understanding is that when using the Outlook app on managed devices, it appears as “Outlook for iOS and Android” in Exchange is due to its proxy model with EAS.
This can cause MDMs (Intune/AirWatch) to list it as unmanaged.
Workarounds depending on your objective:
Use Intune App Protection Policies to secure Outlook data without relying on device recognition.
Set MDM alerts for devices recognized as “Outlook for iOS and Android” to address them promptly.
Provide feedback to Microsoft for potential changes in future updates.
Do you have any additional details so I can better understand your environment? In case there is something I’m missing
LikeLike