Let’s try to reduce the attack vectors, I’ll walk you through the practical remedies and reduction of attack vectors you can do; now.
Turn off SMB 1
Why? Because WannaCry utilizes the exploit, and unless you are on XP or 2003, you have no use for SMB1, and will be using SMB2/SMB3.
To disable SMBv1 on the SMB server, run the following cmdlet:
Windows 8 and Windows Server 2012
Set-SmbServerConfiguration -EnableSMB1Protocol $false
Windows 7, Windows Server 2008 R2 and Windows Vista
Set-ItemProperty -Path “HKLM:\SYSTEM\CurrentControlSet\Services\LanmanServer\Parameters” SMB1 -Type DWORD -Value 0 -Force
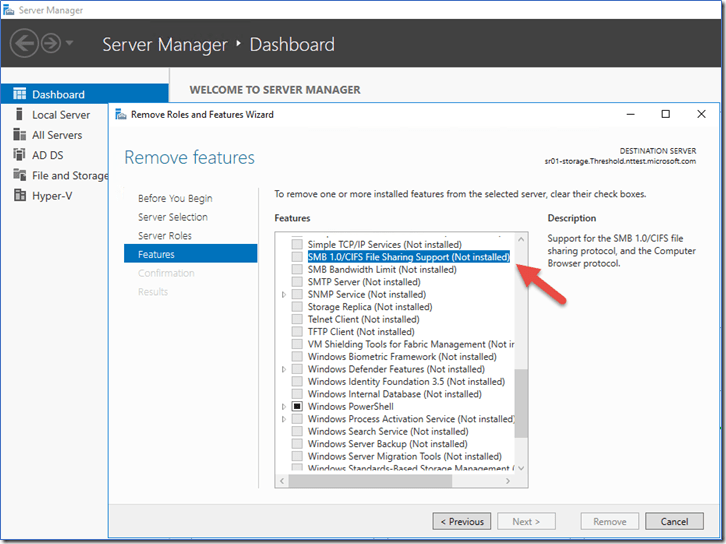
Remove-WindowsFeature FS-SMB1
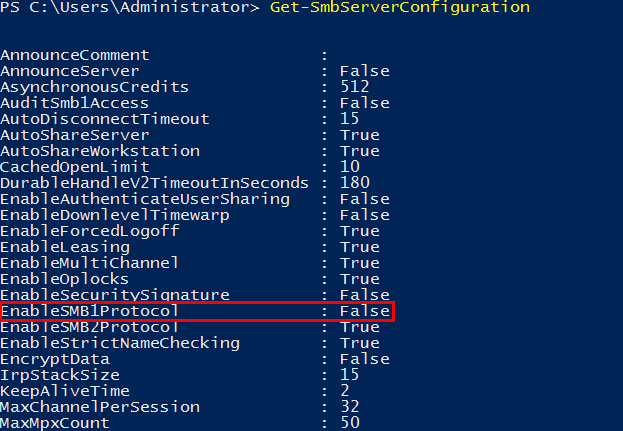
If you want to check whether or not SMB 1.0 is active on your server you can run:
Get-SmbServerConfiguration
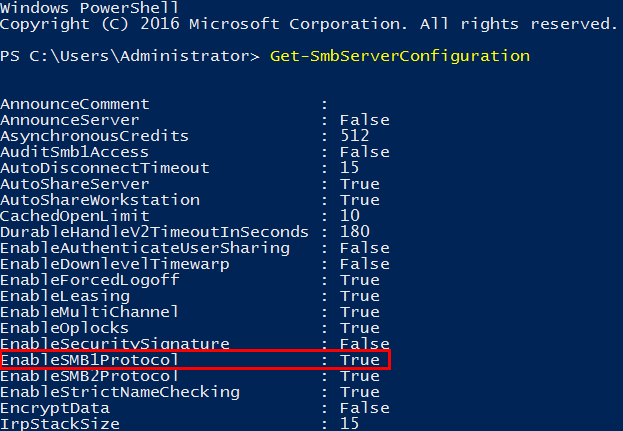
As you can see it states that EnableSMB1Protocol is currently True we want to set this to False.
We can accomplish this by running the following snippet:
Set-SmbServerConfiguration -EnableSMB1Protocol $false -Force’ cmdlet, as shown below.
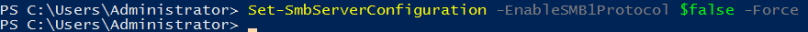
(Force is added to prevent it from pausing for confirmation, and run through.)
Let’s run this again to see if the configuration changed:
Get-SmbServerConfiguration
It is now set to false.
Patch your clients and servers.
WannaCrypt takes advantage of the MS17-010 vulnerability also known as the SMBv1 vulnerability, thankfully it has been patched with MS17-010. Depending on your patch regime, you should expedite and ensure that this patch goes through.
If your systems have been affected; DOUBLEPULSAR will have also been installed, so this will need to also be removed. A script is available (by COUNTERCEPT) that can remotely detect and remove the DOUBLEPULSAR backdoor.