It’s Summer, the heat in Norway and most of the world is unreal these days with world records being broken. We are in the middle of 2018, and a lot has happened!
I joined Lumagate in March as a Principal Solution Architect, and in May the rebranding to Innofactor was completed which was celebrated with an event called Inspirit that was held in Helsinki.

Innofactor is a leading provider of digitalization and cloud solutions in the Nordic countries. Our task is to help our customers digitalize their business, promote a collaborative way of working, and develop their business processes by utilizing data-driven decision making and secure cloud services. Together with our customers, partners, employees, and investors we produce solutions that help our customers and society to succeed.
If you are looking for a place where you can work with cutting-edge technology, good colleagues and exciting days, you should definitely check us out.
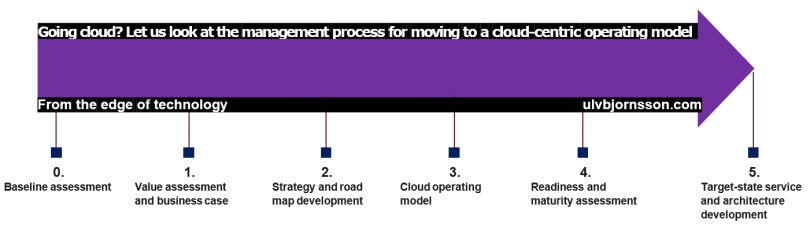
On the 7th of June, I spoke at GNIST, a cloud seminar put-together by Innofactor. Primed on cloud computing, there were a lot of exciting speakers and topics. I was asked to hold a session, and I did one called “A recipe for Cloud Migration” where I covered getting control over operational costs, increasing workforce productivity and driving business agility by moving to Cloud.
If you are holding an event and have a call for content or speakers, let me know. I’ll check it out, and I can if you want also forward it to other relevant speakers based on topic and audience.

Also at the start of July, I was announced as an Alibaba Cloud Most Valuable Professional which I am incredibly humbled by and appreciative to be recognised by Alibaba Cloud for doing the things I love. Nothing is more rewarding than to be able to do what I’m passionate about technology, security and the intersection of it all with the human element. There is no doubt that Alibaba Cloud is the go-to cloud for anyone looking to have a presence in mainland China.

2018 has been a year to symbolise new beginnings and challenges which I am thoroughly enjoying. Working a lot with governance for enterprise organizations as well as hosters in the Nordics and massive datacenter migrations to cloud, I’m looking forward to writing more on this going forward and sharing my insight as well as hearing from you; what your thoughts, gotchas, questions or pitfalls you’d like to ask about or share.

Enjoy the summer and remember to stay hydrated!
If there are any topics or areas you’d like me to focus on, don’t hesitate to let me know! As always you can reach me at @UlvBjornsson, via the comments or by connecting with me on LinkedIn.








 Coco Framework, is
Coco Framework, is